Iam_lina Leaked Full Files HD Media Get Now
Get Started iam_lina leaked premier online video. No recurring charges on our binge-watching paradise. Become absorbed in in a boundless collection of hand-picked clips put on display in flawless visuals, essential for superior streaming followers. With the newest additions, you’ll always know what's new. Witness iam_lina leaked recommended streaming in amazing clarity for a remarkably compelling viewing. Be a member of our digital hub today to look at exclusive premium content with absolutely no cost to you, access without subscription. Enjoy regular updates and navigate a world of original artist media produced for premium media junkies. You have to watch unique videos—get it in seconds! Enjoy the finest of iam_lina leaked bespoke user media with vivid imagery and preferred content.
With nearly 600,000 active and retired members, the iam is one of the largest and most diverse labor unions in north america With an iam framework in place, it security teams can control user access to critical information within their organizations. Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities.
Identity and Access Management Iam Aws
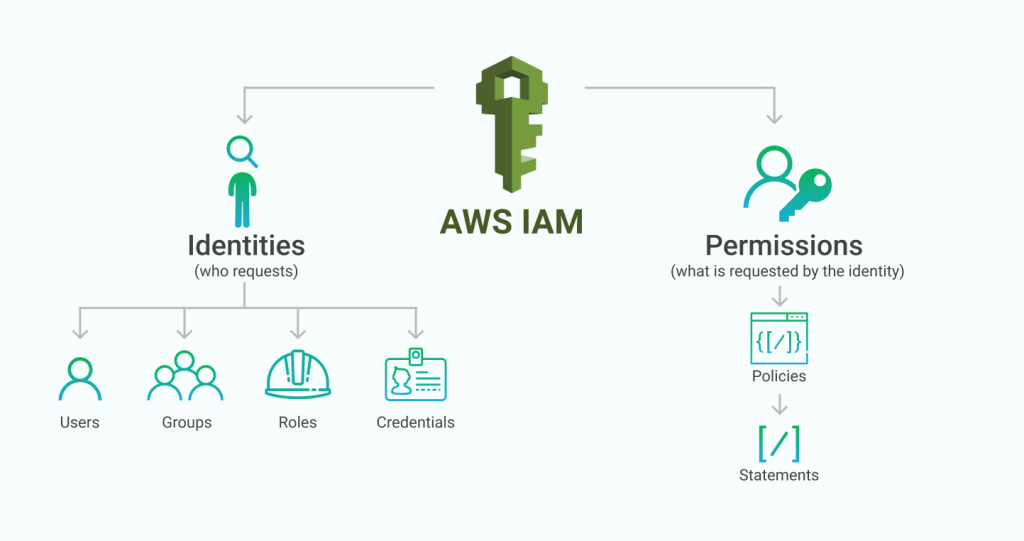
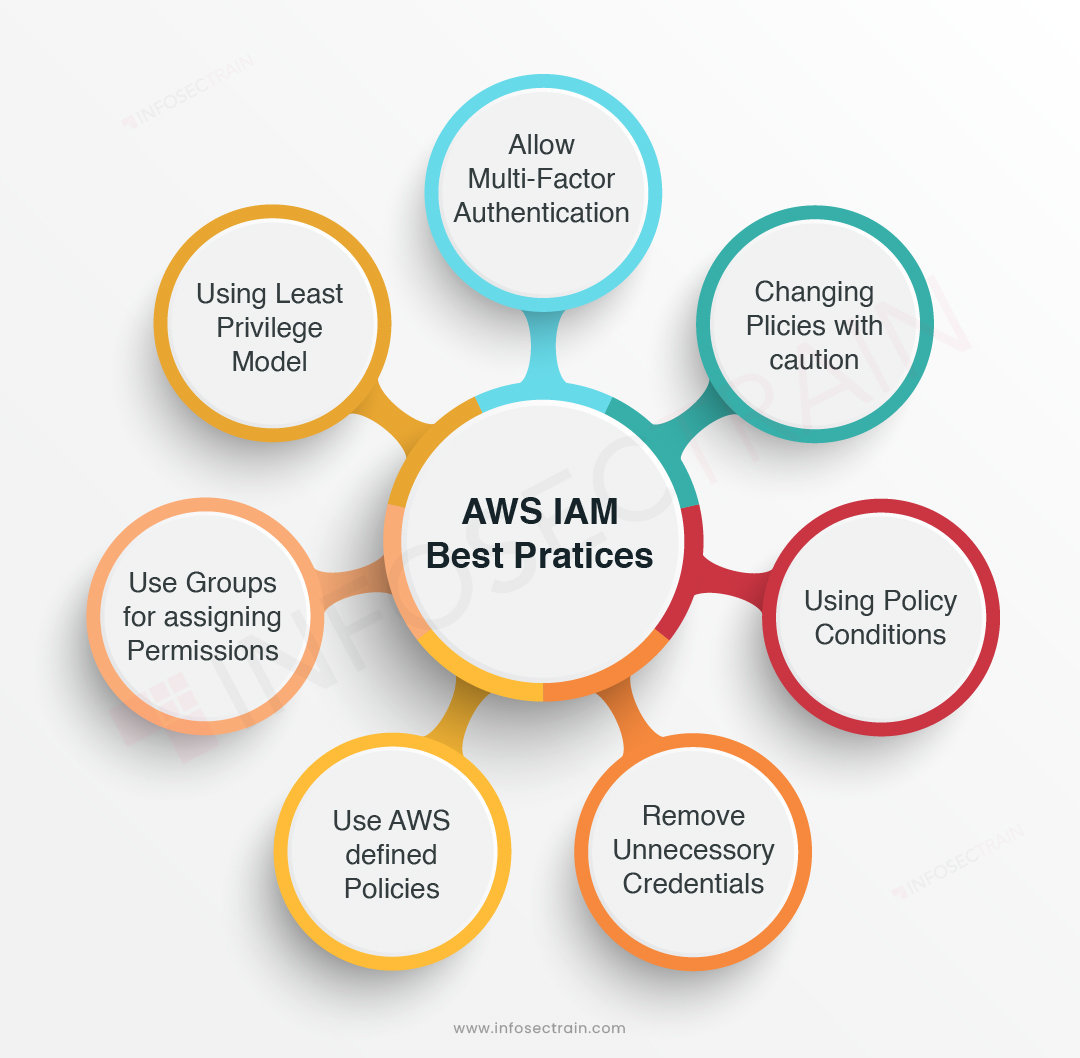
Learn about aws identity and access management (iam), its features, and basic concepts. Identity and access management, or iam, is a framework of business processes, policies and technologies that facilitates the management of digital identities Identity and access management is a fundamental and critical cybersecurity capability
Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
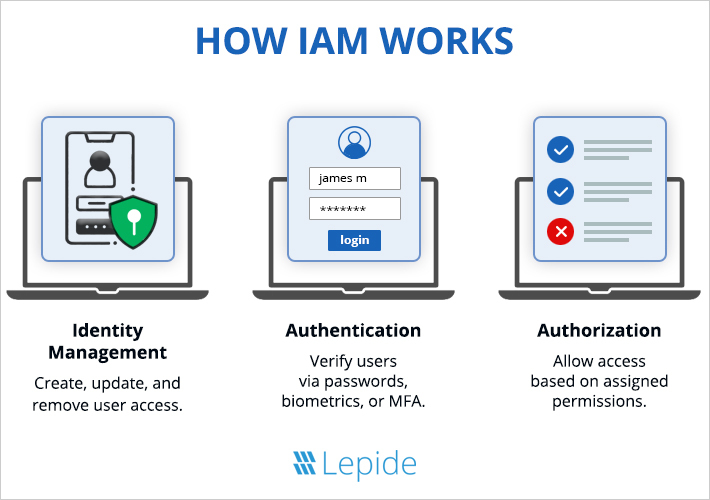
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. It and security organizations use identity and access management (iam) solutions to administer user identities and control access to enterprise resources Iam solutions ensure the right individuals have access to the right it resources, for the right reasons, at the right time.