Iam_nailah Nude Full Collection Videos & Photos Download
Access Now iam_nailah nude prime webcast. 100% on us on our media destination. Get lost in in a broad range of hand-picked clips brought to you in unmatched quality, a must-have for passionate watching fans. With newly added videos, you’ll always remain up-to-date. pinpoint iam_nailah nude tailored streaming in ultra-HD clarity for a remarkably compelling viewing. Enter our content collection today to check out content you won't find anywhere else with completely free, registration not required. Be happy with constant refreshments and delve into an ocean of one-of-a-kind creator videos engineered for first-class media addicts. You have to watch unique videos—get a quick download! Enjoy top-tier iam_nailah nude exclusive user-generated videos with brilliant quality and chosen favorites.
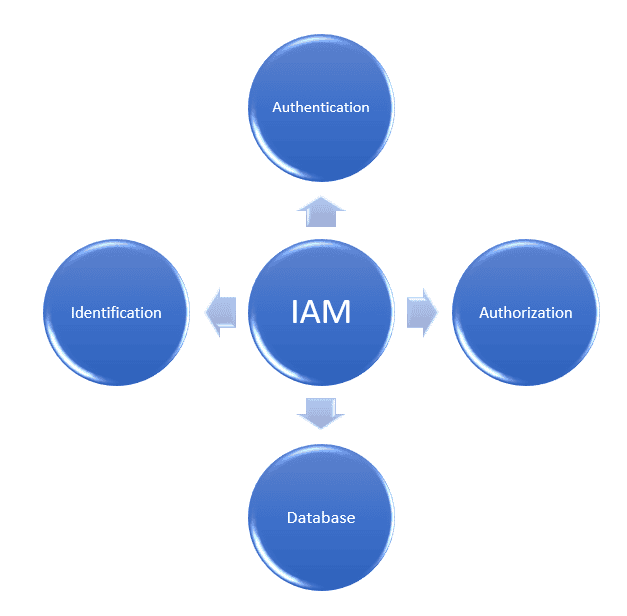
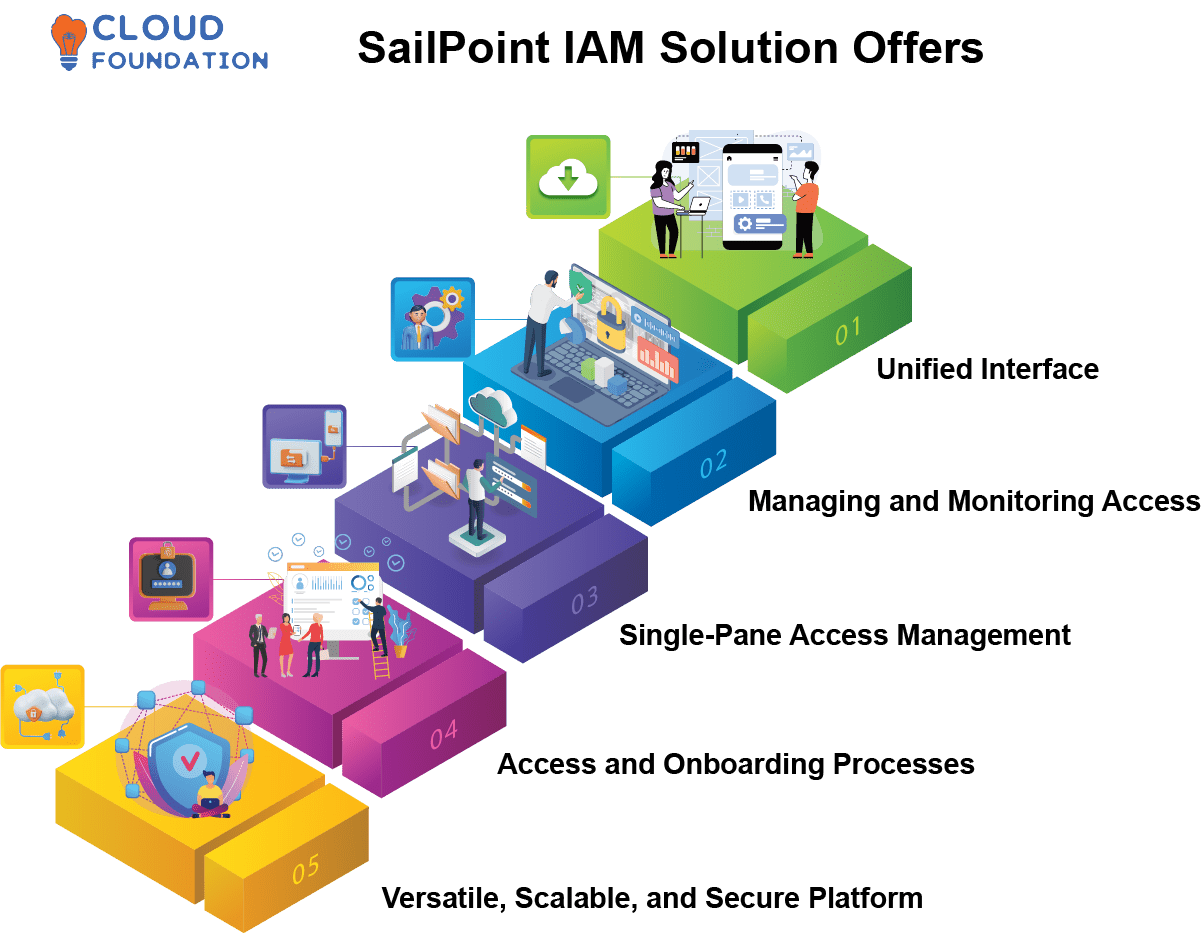
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively. Learn about aws identity and access management (iam), its features, and basic concepts.
テクニカルトレーナーと学ぶ AWS IAM ロール ~ ここが知りたかった ! つまずきやすい部分を理解してモヤっとを解消
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Identity and access management, or iam, is a foundational component of virtually any modern application environment. Identity and access management is a fundamental and critical cybersecurity capability
Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity.