Iam_katy Onlyfans Full Files Video & Foto Get Now
Claim Your Access iam_katy onlyfans top-tier on-demand viewing. No wallet needed on our entertainment portal. Surrender to the experience in a massive assortment of featured videos put on display in best resolution, tailor-made for deluxe watching admirers. With fresh content, you’ll always be ahead of the curve. Browse iam_katy onlyfans hand-picked streaming in gorgeous picture quality for a truly engrossing experience. Register for our digital space today to browse VIP high-quality content with free of charge, no subscription required. Receive consistent updates and investigate a universe of indie creator works designed for premium media buffs. Take this opportunity to view unseen videos—download immediately! Witness the ultimate iam_katy onlyfans unique creator videos with lifelike detail and staff picks.
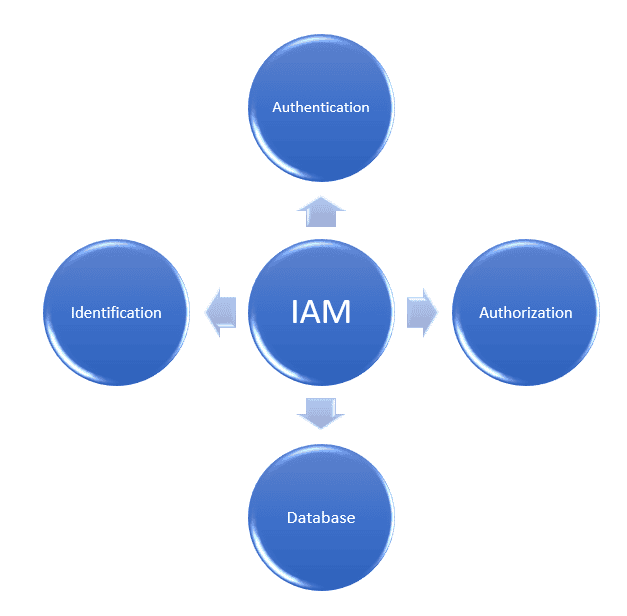
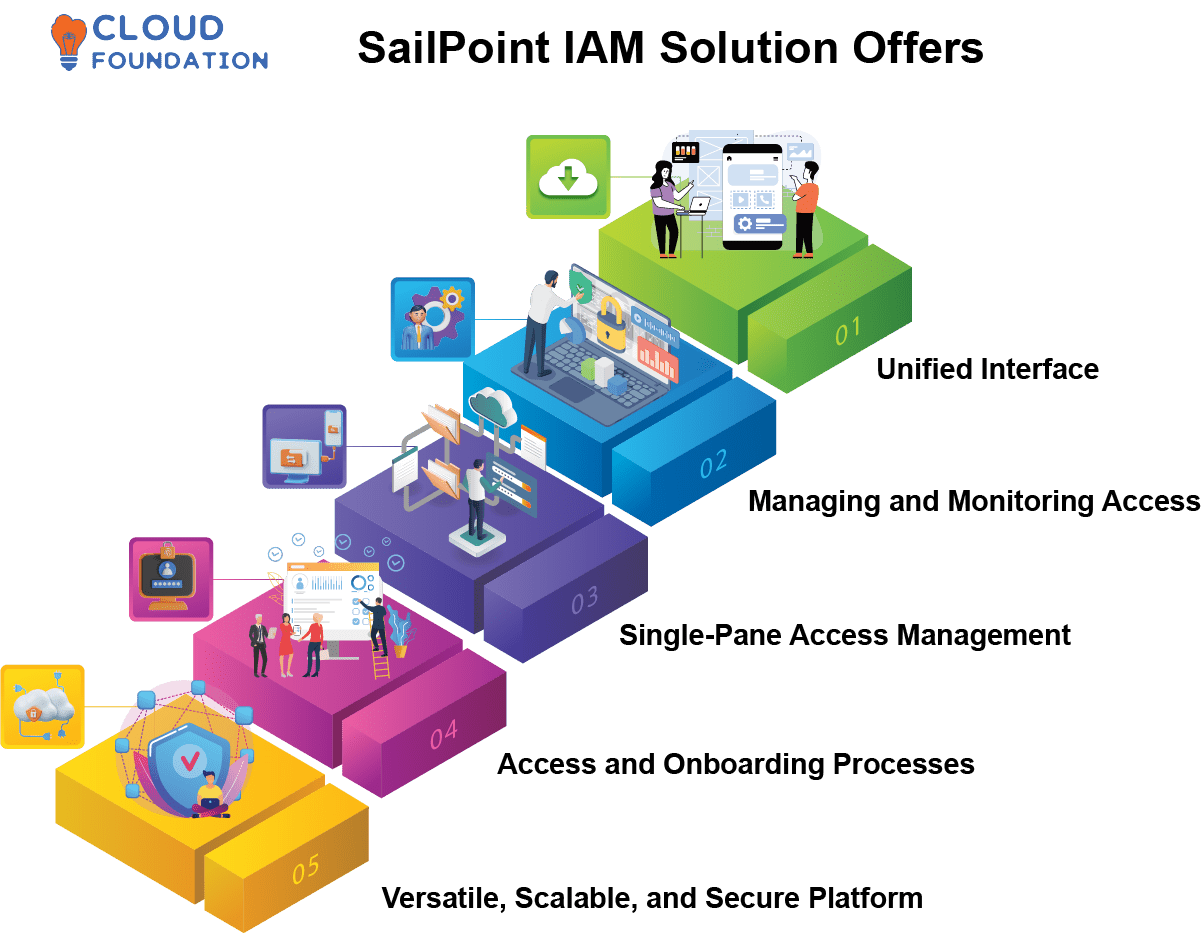
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) verifies user identities and controls resource access, a core component of zero trust security Learn about aws identity and access management (iam), its features, and basic concepts.
What is Attribute-Based Access Control (ABAC)? – A Complete Guide
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. You’ll learn about the iam framework, the benefits and risks of implementing iam solutions, and implementation best practices. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time.
Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management is the framework and processes organizations use to manage and secure digital identities and control user access to critical information In this article, we’ll review what identity and access management (iam or idam) is, why it’s important, and how it compares with other access management concepts