"iam_emiliagomez" Nude Digital Vault All Files Full Link
Get Started "iam_emiliagomez" nude prime digital media. 100% on us on our entertainment center. Step into in a ocean of videos of series available in superb video, optimal for passionate viewing enthusiasts. With content updated daily, you’ll always know what's new. Locate "iam_emiliagomez" nude organized streaming in incredible detail for a genuinely engaging time. Enroll in our viewing community today to view private first-class media with no payment needed, no credit card needed. Stay tuned for new releases and venture into a collection of one-of-a-kind creator videos crafted for top-tier media supporters. Don’t miss out on unseen videos—download now with speed! Enjoy the finest of "iam_emiliagomez" nude original artist media with dynamic picture and featured choices.
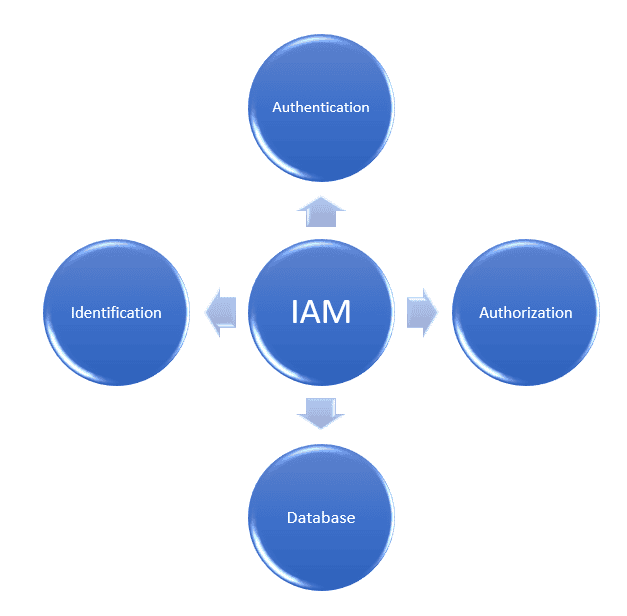
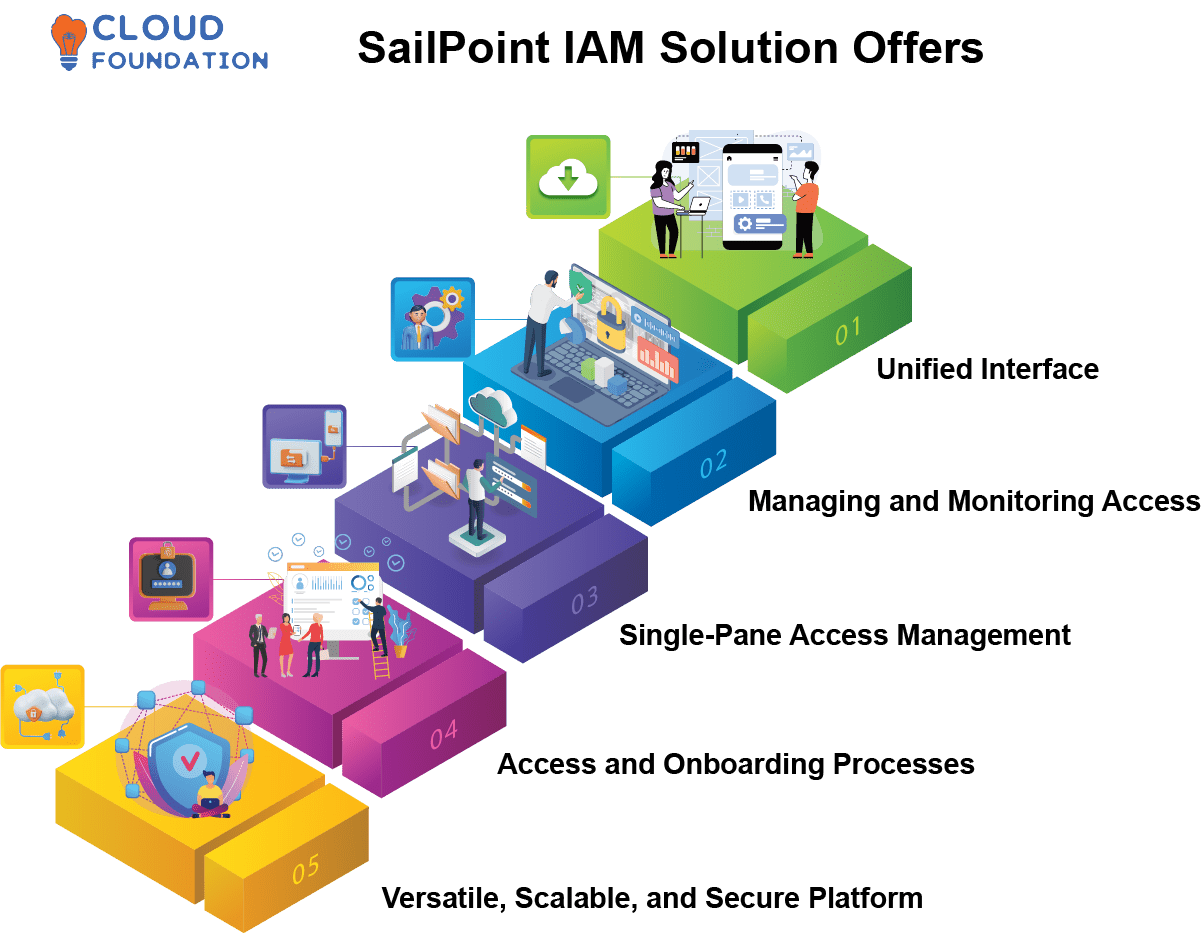
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. With an iam framework in place, it security teams can control user access to critical information within their organizations. Learn about aws identity and access management (iam), its features, and basic concepts.
What Is Identity and Access Management? | Baeldung on Computer Science
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Identity and access management, or iam, is a framework of business processes, policies and technologies that facilitates the management of digital identities Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information.
Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. It and security organizations use identity and access management (iam) solutions to administer user identities and control access to enterprise resources Iam solutions ensure the right individuals have access to the right it resources, for the right reasons, at the right time. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity.
Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.