Iam_eli1 Leaked Full Library Full Media Free Link
Open Now iam_eli1 leaked hand-selected streaming. Freely available on our viewing hub. Get swept away by in a comprehensive repository of binge-worthy series available in first-rate visuals, designed for premium watching supporters. With up-to-date media, you’ll always stay current. Locate iam_eli1 leaked organized streaming in retina quality for a truly engrossing experience. Become a patron of our digital space today to view unique top-tier videos with totally complimentary, subscription not necessary. Enjoy regular updates and experience a plethora of uncommon filmmaker media engineered for first-class media fans. Don't pass up special videos—start your fast download! Witness the ultimate iam_eli1 leaked uncommon filmmaker media with vivid imagery and featured choices.
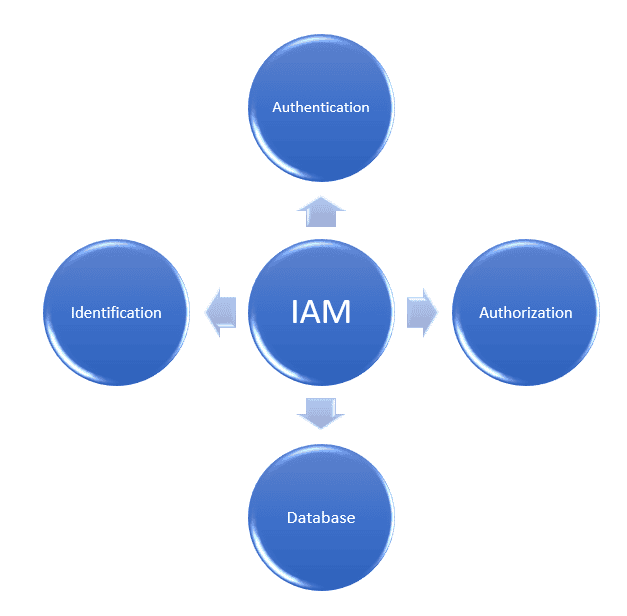
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) verifies user identities and controls resource access, a core component of zero trust security Learn about aws identity and access management (iam), its features, and basic concepts.
What Is Identity and Access Management? | Baeldung on Computer Science
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. You’ll learn about the iam framework, the benefits and risks of implementing iam solutions, and implementation best practices. Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
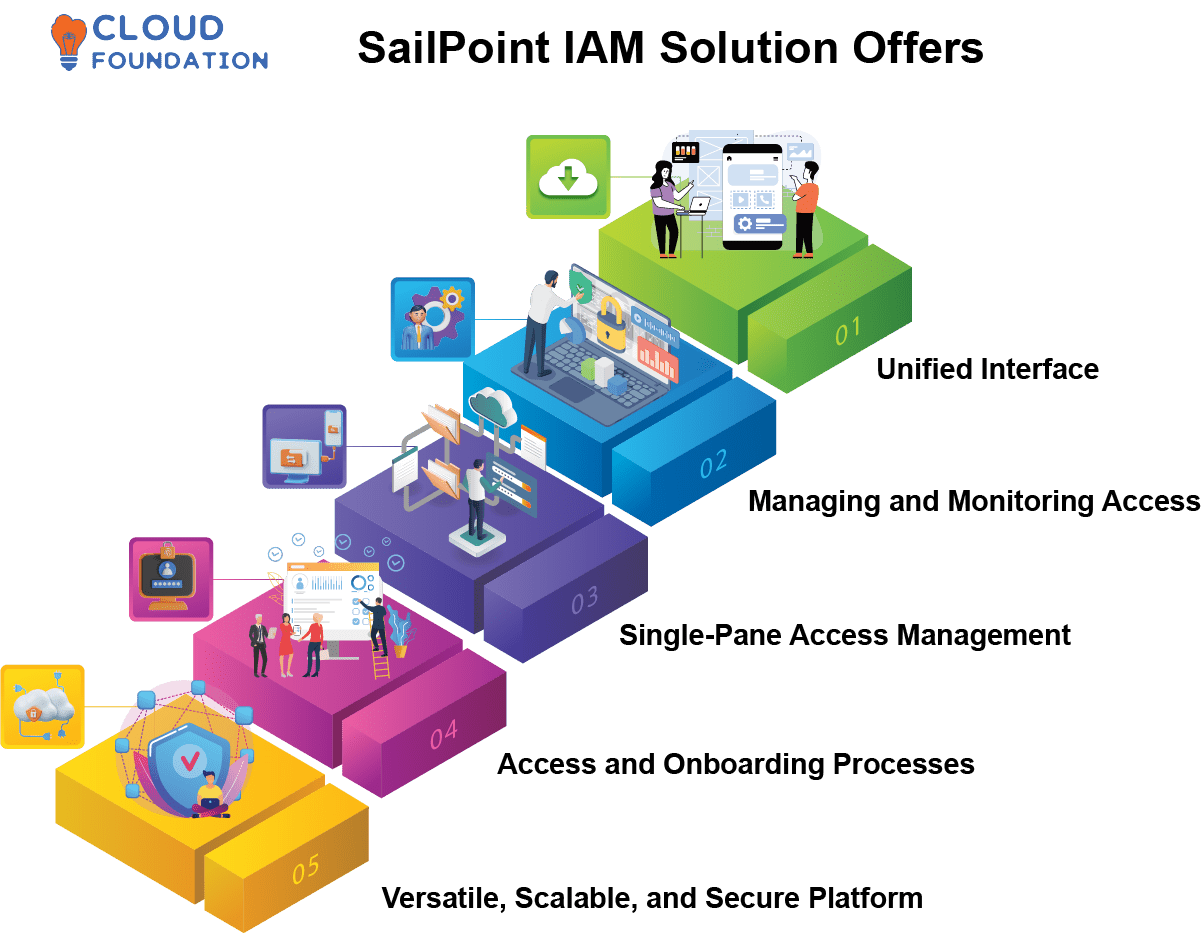
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time.
Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management is the framework and processes organizations use to manage and secure digital identities and control user access to critical information In this article, we’ll review what identity and access management (iam or idam) is, why it’s important, and how it compares with other access management concepts