Iam.clara Nude 2026 Vault Video & Foto Direct
Begin Your Journey iam.clara nude superior online video. 100% on us on our video archive. Plunge into in a extensive selection of selections highlighted in superior quality, flawless for prime viewing enthusiasts. With content updated daily, you’ll always receive updates. Locate iam.clara nude expertly chosen streaming in impressive definition for a absolutely mesmerizing adventure. Access our digital space today to see select high-quality media with at no cost, no need to subscribe. Get fresh content often and experience a plethora of distinctive producer content produced for top-tier media followers. Make sure to get never-before-seen footage—swiftly save now! Witness the ultimate iam.clara nude special maker videos with exquisite resolution and hand-picked favorites.
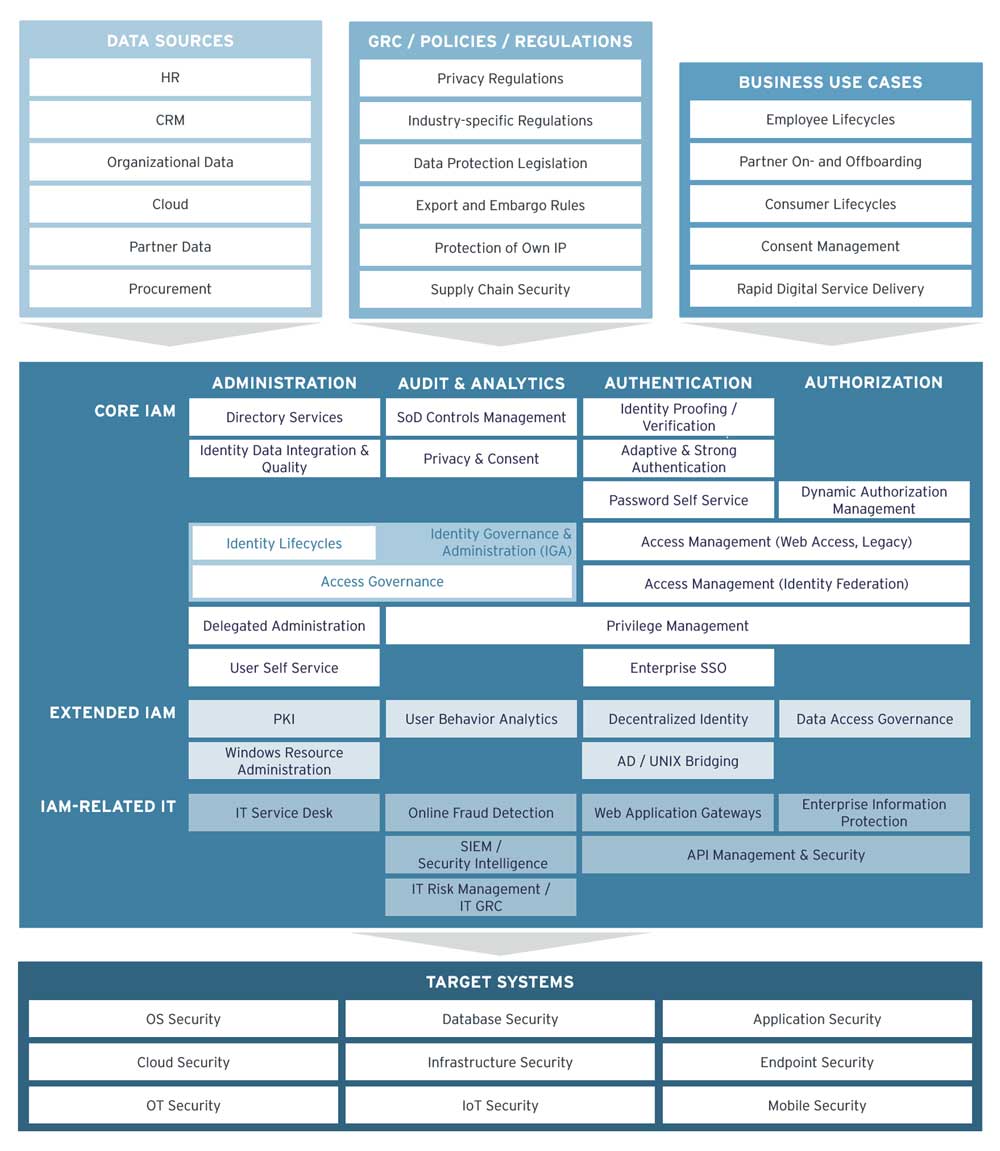
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management is the framework and processes organizations use to manage and secure digital identities and control user access to critical information With iam, you can manage permissions that control which aws resources users can access
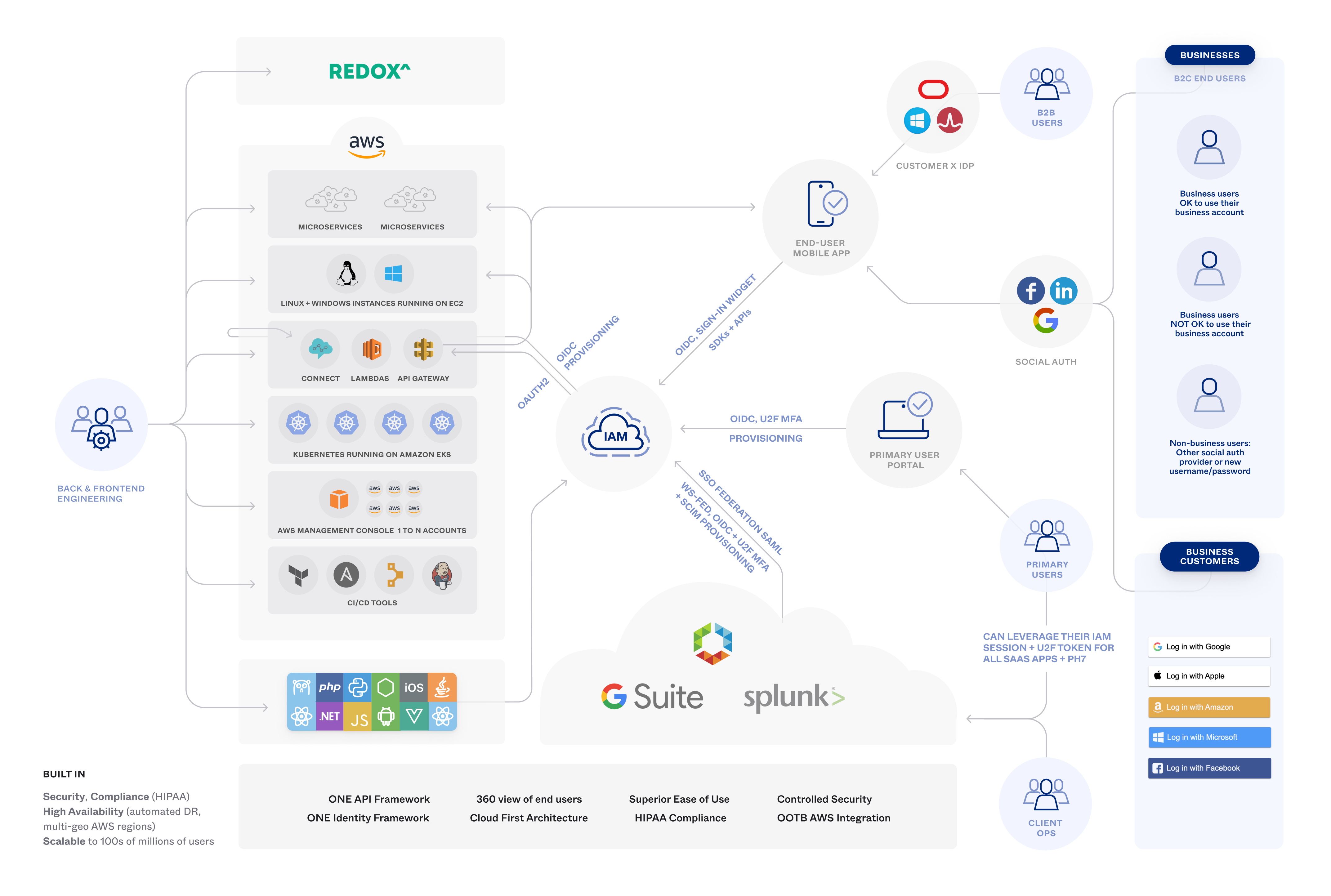
Onelogin Workforcecustomer Identity Access Management
You use iam to control who is authenticated (signed in) and authorized (has permissions) to use resources. Identity and access management, or iam, is a foundational component of virtually any modern application environment. Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms.
Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information.
Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity.