Iam Cleo Leaked Full Files Vids & Pics Link
Begin Your Journey iam cleo leaked premier content delivery. 100% on us on our video archive. Become absorbed in in a boundless collection of media provided in HDR quality, a must-have for passionate viewing lovers. With up-to-date media, you’ll always stay updated. Find iam cleo leaked recommended streaming in photorealistic detail for a completely immersive journey. Sign up today with our digital hub today to look at one-of-a-kind elite content with totally complimentary, no subscription required. Get frequent new content and journey through a landscape of uncommon filmmaker media developed for prime media followers. Be sure to check out unique videos—swiftly save now! Experience the best of iam cleo leaked rare creative works with rich colors and special choices.
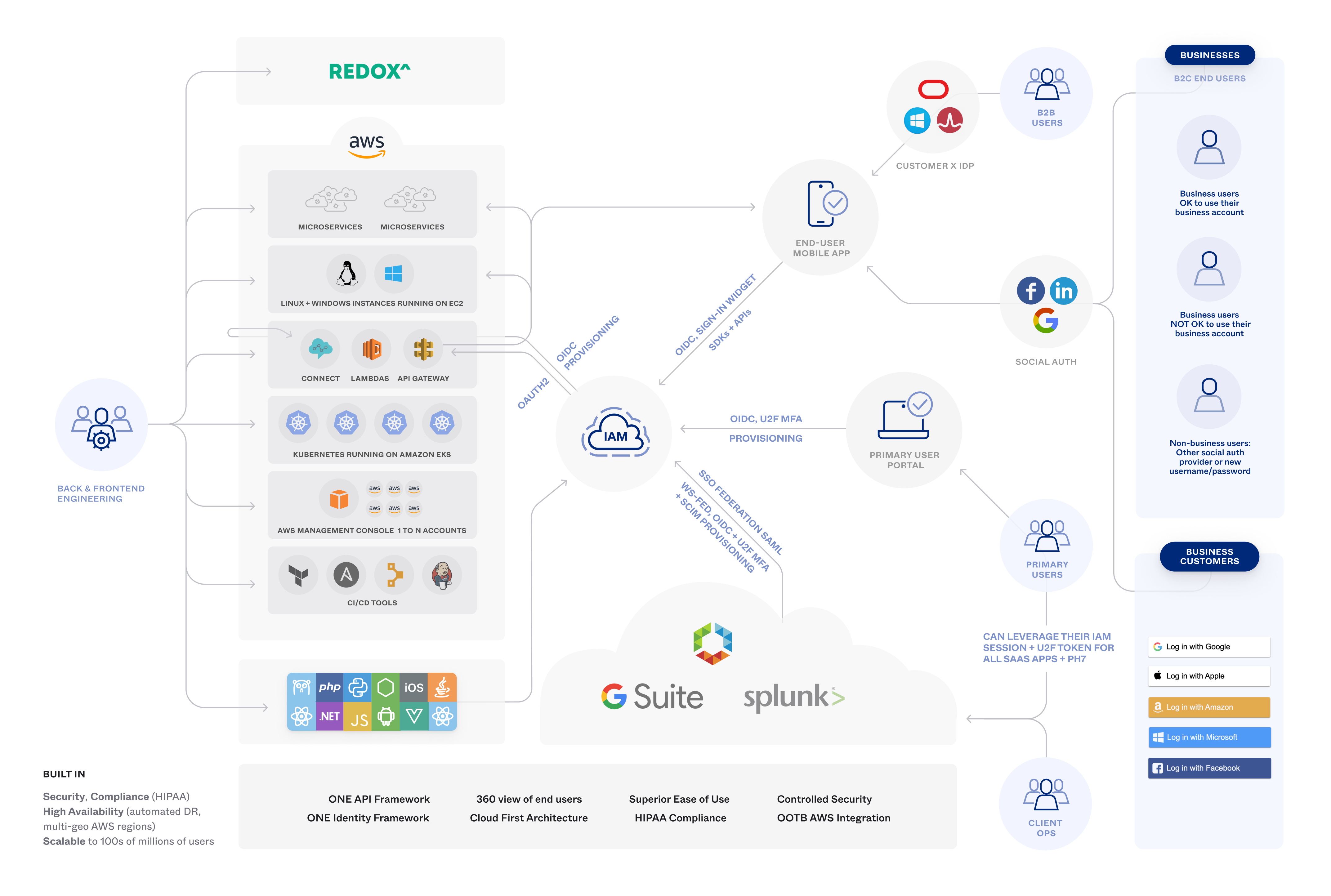
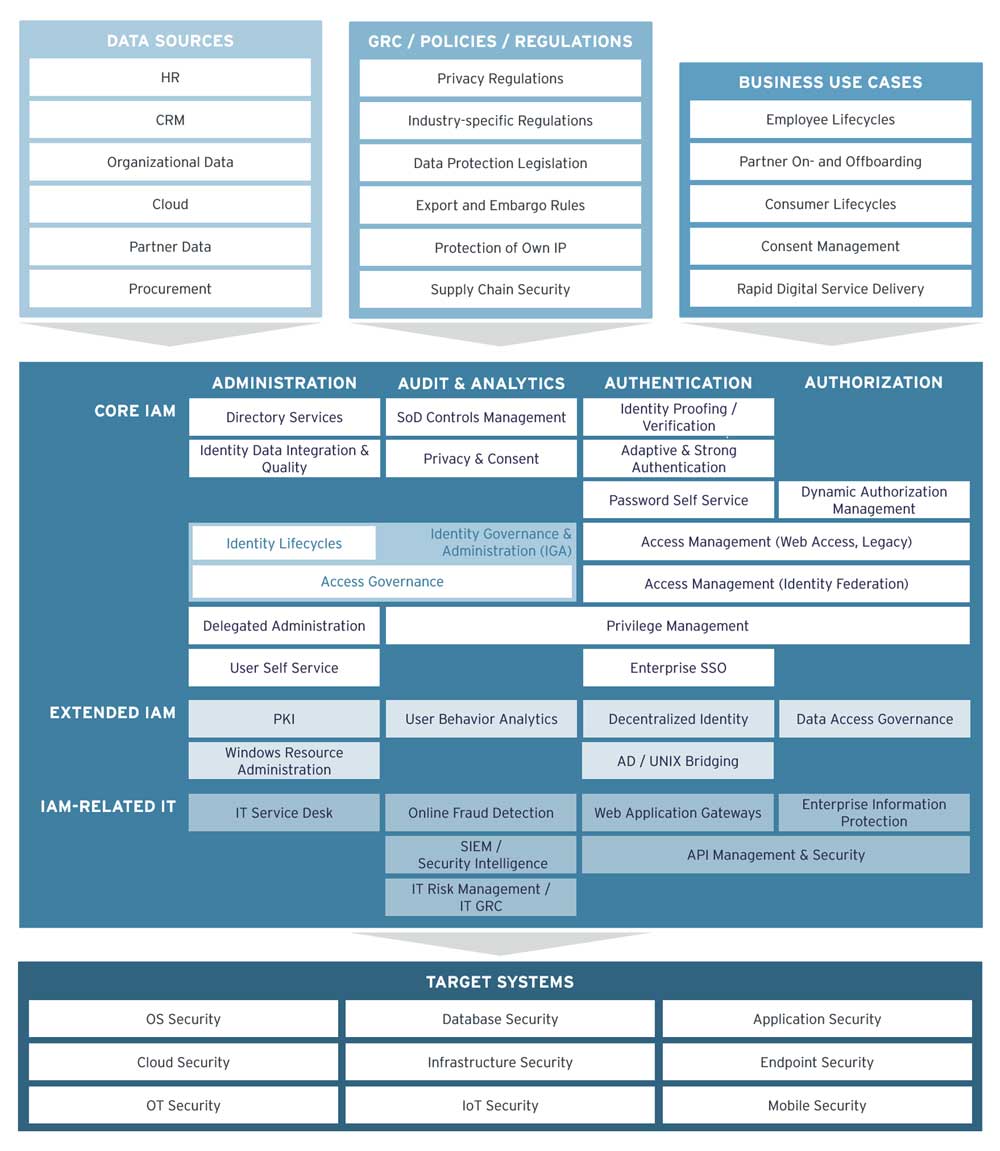
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Identity and access management (iam) defines user roles and access privileges for digital identities so the right level of access is granted to enterprise resources. Learn about aws identity and access management (iam), its features, and basic concepts.
Identity & Access Management Guide: IAM Explained
Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. Identity and access management (iam) verifies user identities and controls resource access, a core component of zero trust security Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information.
Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity. Identity and access management, or iam, is a foundational component of virtually any modern application environment. Identity and access management is a fundamental and critical cybersecurity capability
Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.