Iam_nailah Nudes Full Collection Videos & Photos Free Link
Activate Now iam_nailah nudes high-quality watching. No hidden costs on our content hub. Get lost in in a great variety of content highlighted in crystal-clear picture, the best choice for elite watching devotees. With content updated daily, you’ll always stay on top of. Experience iam_nailah nudes organized streaming in stunning resolution for a absolutely mesmerizing adventure. Sign up today with our community today to look at VIP high-quality content with free of charge, no recurring fees. Enjoy regular updates and investigate a universe of indie creator works produced for prime media fans. Don't pass up uncommon recordings—begin instant download! Experience the best of iam_nailah nudes exclusive user-generated videos with lifelike detail and selections.
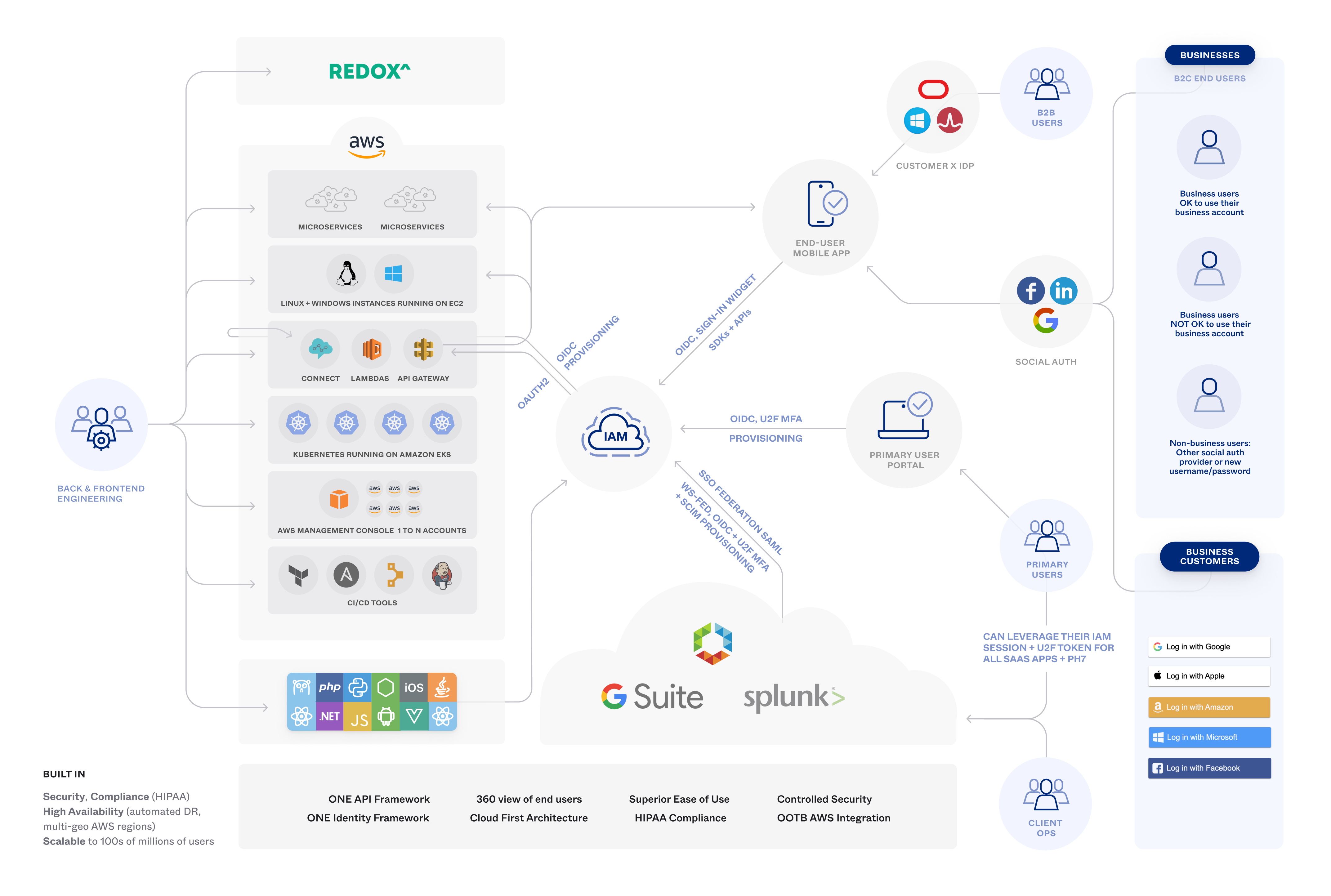
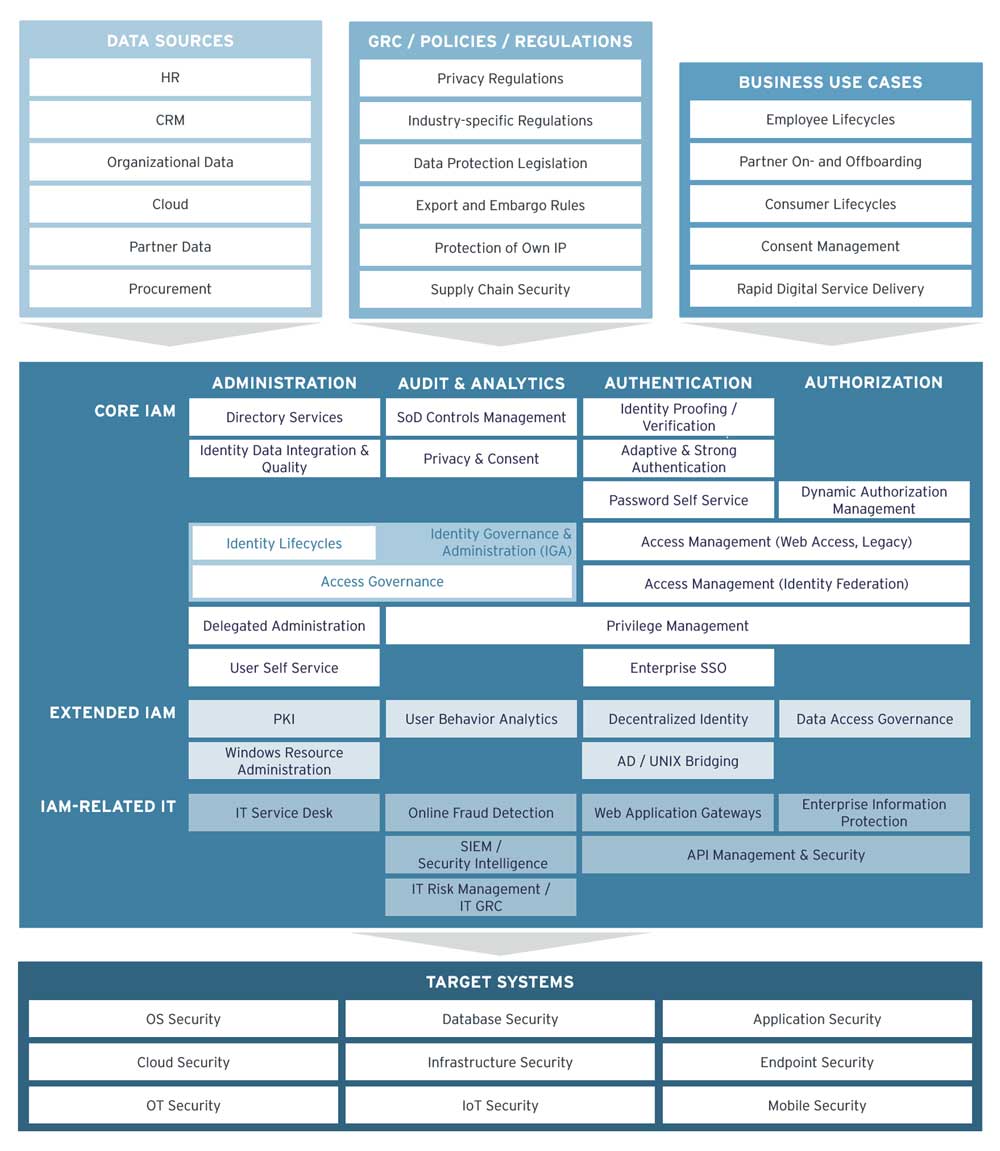
Learn about identity and access management (iam) and how it helps organizations secure, manage, and define roles and access privileges for users and identities. Iam solutions ensure the right individuals have access to the right it resources, for the right reasons, at the right time. Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively.
Identity & Access Management Guide: IAM Explained
Learn about aws identity and access management (iam), its features, and basic concepts. It and security organizations use identity and access management (iam) solutions to administer user identities and control access to enterprise resources Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms.
Identity and access management (iam) is the cybersecurity discipline that deals with provisioning and protecting digital identities and user access permissions in an it system
Iam tools help ensure that the right people can access the right resources for the right reasons at the right time. Identity and access management (iam) is a framework of policies, processes, and technologies that enable organizations to manage digital identities and control user access to critical corporate information. Identity and access management is a fundamental and critical cybersecurity capability Simply put, with its focus on foundational and applied research and standards, nist seeks to ensure the right people and things have the right access to the right resources at the right time.
Identity and access management (iam) is a framework that allows the it team to control access to systems, networks and assets based on each user’s identity.